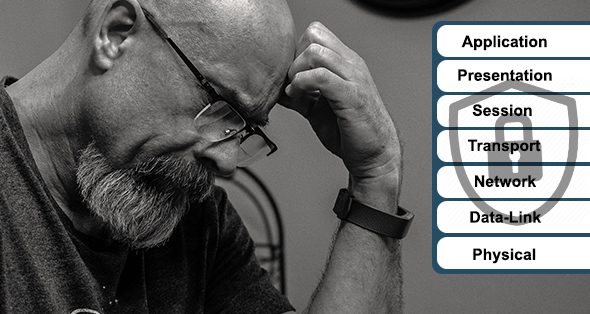
A major concern in the niche cybersecurity field of DevSecOps is microservices and container security. Just as true in cybersecurity as it is in athletics, building and maintaining great defense lifts an operation out of constant “fire-fighting” mode and up to a place where it can be proactive about growing the business. The thing to remember is that great cybersecurity begins with great security planning. As Benjamin Franklin advised, “A failure to plan is a plan to fail.”